Vulnerabilities/Malwares
Chinese hackers use VMware’s zero-day vulnerability to bypass Linux and Windows systems.

Vulnerabilities/Malwares
In recent attacks, MetaStealer malware targets Apple macOS.
Vulnerabilities/Malwares
The Apple zero-click iMessage Exploit that spread spyware to iPhones
Vulnerabilities/Malwares
Google fixes one more Chrome zero-day vulnerability exploited by Hackers
-

 Ethical Hacking/Pen Testing3 years ago
Ethical Hacking/Pen Testing3 years agoSquarePhish: QR Code and Auth Device Code authentication Phishing tool
-

 Vulnerabilities/Malwares3 years ago
Vulnerabilities/Malwares3 years agoHyundai and Kia patch a bug that allowed USB cable car thefts.
-

 Ethical Hacking/Pen Testing4 years ago
Ethical Hacking/Pen Testing4 years agoHackBrowserData: Decrypt passwords/cookies/history/bookmarks from the browser
-

 Malwares3 years ago
Malwares3 years agoCybercriminals Use the Powerful BatCloak Engine to make malware undetected by AntiVirus
-

 Windows/Mac/Linux4 years ago
Windows/Mac/Linux4 years agoGoogle caught North Korean Hackers Using Chrome Browser Exploit on Americans
-

 Cyber Attacks/Data Breaches4 years ago
Cyber Attacks/Data Breaches4 years agoHackers from the Russian Federation have continued to launch attacks on Ukrainian organisations with info-stealer malware.
-

 Mobile Hacking3 years ago
Mobile Hacking3 years agoWhatsApp now supports proxy servers to bypass government restrictions.
-

 Ethical Hacking/Pen Testing3 years ago
Ethical Hacking/Pen Testing3 years agoRemotely exploiting Android devices using ADB (Android Debug Bridge) and Metasploit-Framework.

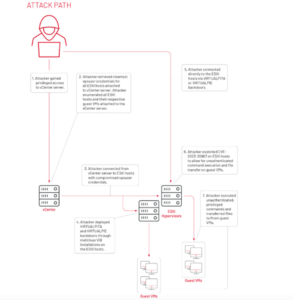 It has been discovered that UNC3886, a group sponsored by China, can take advantage of a zero-day vulnerability in VMware ESXi hosts to backdoor Linux and Windows systems.
It has been discovered that UNC3886, a group sponsored by China, can take advantage of a zero-day vulnerability in VMware ESXi hosts to backdoor Linux and Windows systems.