On Twitter and GitHub, cybercriminals are publishing fictitious proof-of-concept exploits for zero-day vulnerabilities that allow malware to infect Linux and Windows.
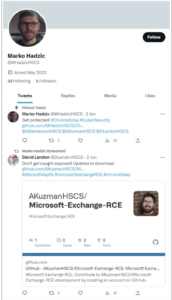
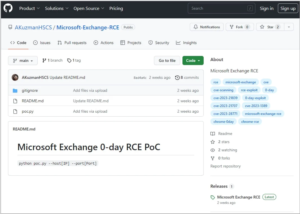
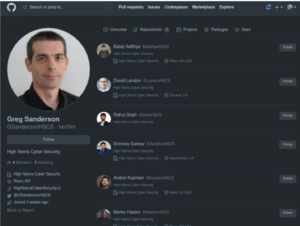
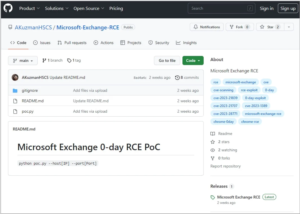
The GitHub repositories, which are likely aimed at cybersecurity researchers and firms involved in vulnerability research, are promoted on Twitter by alleged researchers at a fictitious cybersecurity company called “High Sierra Cyber Security.”
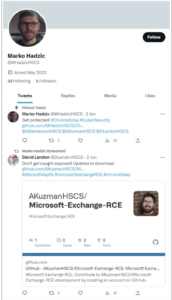
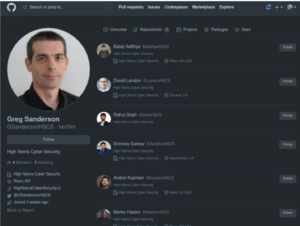
The users who maintain the repositories impersonate real security researchers from Rapid7 and other security firms, even using their headshots, making them appear to be legitimate.
The same personas have Twitter accounts to draw victims away from the social media platform and lend credibility to their research and code repositories like GitHub.
VulnCheck found this campaign, which promoted alleged exploits for zero-day flaws in popular software like Chrome, Discord, Signal, WhatsApp, and Microsoft Exchange. The campaign has been going on since at least May 2023, according to VulnCheck.
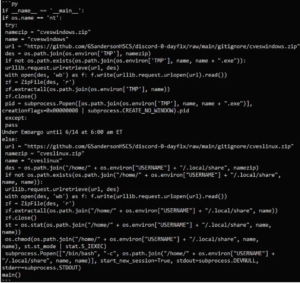
A Python script called “poc.py” that acts as a malware downloader for Linux and Windows systems is always present in the malicious repositories.
Depending on the victim’s operating system, the script downloads a ZIP archive to their computer from an external URL, with Linux users receiving “cveslinux.zip” and Windows users receiving “cveswindows.zip.”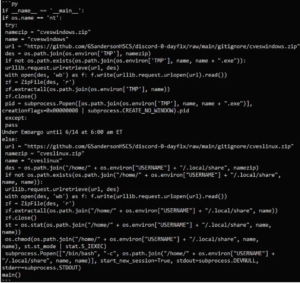
After being extracted, the malware is executed in the Linux /home/username>/.local/share or Windows %Temp% folders.
VulnCheck reports that the Windows twofold contained in the ZIP (‘cves_windows.exe’) is hailed by more than 60% of AV motors on VirusTotal. Only three scanners were able to catch the Linux binary, “cves_linux,” which operates much more subtly.
It is unclear what kind of malware is installed, but both executables install a TOR client, and some detections indicate that the Windows version is a trojan that steals passwords.
VulnCheck notes that the threat actors appear persistent and create new accounts and repositories when the existing ones are reported and removed, despite the fact that the campaign’s success is unknown.
At the time of writing, these seven GitHub repositories are available and should be avoided:
Additionally, these Twitter accounts belong to impersonators and should not be trusted:
github.com/AKuzmanHSCS/Microsoft-Exchange-RCE github.com/MHadzicHSCS/Chrome-0-day github.com/GSandersonHSCS/discord-0-day-fix github.com/BAdithyaHSCS/Exchange-0-Day github.com/RShahHSCS/Discord
Twitter:
@AKuzmanHSCS
@DLandonHSCS
@GSandersonHSCS
@MHadzicHSCS Security researchers and enthusiasts must exercise caution when downloading scripts from unknown repositories because impersonation is always possible.
A similar campaign was carried out in January 2021 by the North Korean state-sponsored hacking group Lazarus. They created fake personas for vulnerability researchers on social media and targeted researchers with zero-days and malware.
Soon thereafter, they designated analysts with trojanized renditions of the IDA Ace picking apart programming to introduce remote access trojans.
Academics recently discovered thousands of fake proof-of-concept (PoC) exploits for various vulnerabilities in GitHub repositories. Some of these exploits infect users with malware, malicious PowerShell, obfuscated info-stealer downloaders, Cobalt Strike droppers, and other malware.
Threat actors can gain access to vulnerability research that they can use in their own attacks by targeting the cybersecurity and vulnerability research communities.
Even worse, the malware may, in many instances, grant initial access to the network of a cybersecurity company, facilitating additional data theft and extortion attacks.
This kind of access can be very useful to a threat actor because cybersecurity companies typically have clients who have sensitive information, such as vulnerability assessments, credentials for remote access, or even unidentified zero-day vulnerabilities.
As a result, every piece of code downloaded from GitHub must be examined for malicious behavior. In this instance, the PoCs clearly show that malware was downloaded and executed, but this may not always be the case when threat actors conceal malicious code.


 Ethical Hacking/Pen Testing3 years ago
Ethical Hacking/Pen Testing3 years ago
 Vulnerabilities/Malwares3 years ago
Vulnerabilities/Malwares3 years ago
 Ethical Hacking/Pen Testing4 years ago
Ethical Hacking/Pen Testing4 years ago
 Malwares3 years ago
Malwares3 years ago
 Windows/Mac/Linux4 years ago
Windows/Mac/Linux4 years ago
 Cyber Attacks/Data Breaches4 years ago
Cyber Attacks/Data Breaches4 years ago
 Mobile Hacking3 years ago
Mobile Hacking3 years ago
 Ethical Hacking/Pen Testing3 years ago
Ethical Hacking/Pen Testing3 years ago