A security scientist was granted a bug abundance of $107,500 for distinguishing security issues in Google Home brilliant speakers that could be taken advantage of to introduce secondary passages and transform them into wiretapping gadgets.
In a technical paper that was released this week, the researcher who goes by the name Matt revealed that the flaws “allowed an attacker within wireless proximity to install a ‘backdoor’ account on the device, enabling them to send commands to it remotely over the internet, access its microphone feed, and make arbitrary HTTP requests within the victim’s LAN.”
In making such malignant solicitations, not exclusively might the Wi-Fi secret phrase at some point get uncovered, yet additionally give the foe direct admittance to different gadgets associated with a similar organization. Google resolved the issues in April 2021 following responsible disclosure on January 8, 2021.
In an assault chain itemized by the scientist, a danger entertainer hoping to snoop on a casualty can fool the person into introducing a vindictive Android application, which, after identifying a Google Home gadget on the organization, issues covert HTTP solicitations to connect an assailant’s record to the casualty’s gadget.
In addition, it was discovered that a Google Home device can be forced into “setup mode” and set up its own open Wi-Fi network by launching a Wi-Fi deauthentication attack to force it to disconnect from the network.
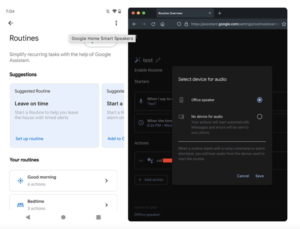
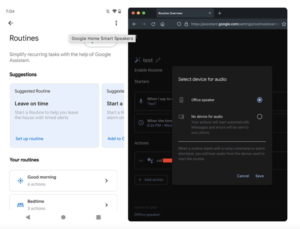
The threat actor can then link their account to the device by connecting to the device’s setup network and requesting information like the device name, cloud_device_id, and certificate.
A successful link process allows the adversary to use Google Home routines to turn the volume down to zero and call a specific phone number at any time to spy on the victim through the device’s microphone, regardless of the attack sequence used.
The issue, in a nutshell, is how a malicious Google user account can be added to a target’s home automation device using the Google Home software architecture.
A threat actor attempting to eavesdrop on a victim can trick the victim into installing a malicious Android app in an attack chain detailed by the researcher. This app then sends stealthy HTTP requests to link an attacker’s account to the victim’s device when it detects a Google Home device on the network.
In addition, it was discovered that a Google Home device can be forced into “setup mode” and set up its own open Wi-Fi network by launching a Wi-Fi deauthentication attack to force it to disconnect from the network.
The threat actor can then link their account to the device by connecting to the device’s setup network and requesting information like the device name, cloud_device_id, and certificate.
A successful link process allows the adversary to use Google Home routines to turn the volume down to zero and call a specific phone number at any time to spy on the victim through the device’s microphone, regardless of the attack sequence used.
According to Matt, “The victim may only notice that the device’s LEDs turn solid blue, but they would probably just assume it’s updating the firmware or something.” There is no indication that the microphone is open because the LEDs do not pulse like they normally do when the device is listening during a call.
In addition, the attack can be expanded to include arbitrary HTTP requests made within the victim’s network, file reading, and the introduction of malicious modifications to the linked device that would be applied upon reboot.
Voice-activated devices have been used in the past to covertly spy on potential targets, and this is not the first time this has been done.
A method known as Light Commands was discovered in November 2019 by a group of academics. Light Commands refers to a flaw in MEMS microphones that enables attackers to remotely inject inaudible and invisible commands using light into popular voice assistants like Google Assistant, Amazon Alexa, Facebook Portal, and Apple Siri.


 Ethical Hacking/Pen Testing3 years ago
Ethical Hacking/Pen Testing3 years ago
 Vulnerabilities/Malwares3 years ago
Vulnerabilities/Malwares3 years ago
 Malwares3 years ago
Malwares3 years ago
 Ethical Hacking/Pen Testing4 years ago
Ethical Hacking/Pen Testing4 years ago
 Windows/Mac/Linux4 years ago
Windows/Mac/Linux4 years ago
 Cyber Attacks/Data Breaches4 years ago
Cyber Attacks/Data Breaches4 years ago
 Mobile Hacking3 years ago
Mobile Hacking3 years ago
 Ethical Hacking/Pen Testing3 years ago
Ethical Hacking/Pen Testing3 years ago